When to bypass authentication
Most connections require credentials — API keys, OAuth tokens, or other authentication methods — to communicate with external systems. However, there are scenarios where authentication is unnecessary or handled outside the platform:- Public APIs: The external system exposes endpoints that do not require authentication.
- IP allowlisting: The target system uses network-level restrictions instead of request-level credentials, allowing traffic from known IP addresses without further authentication.
- Internal services: You are connecting to an internal service within your own infrastructure that does not enforce authentication.
Creating a bypassed connection
You can bypass authentication when creating a new connection for a connector. This creates an authentication method called “No Auth” with the type set to “None - Authentication Bypassed”.Open the New Connection form
Navigate to your connector and select New Connection. Choose the No Auth option under Auth Method to indicate
that no credentials are required.
Configure the connection
Provide a Name and optional Description for the authentication method, then enter the API Base URL for
the target system. This is the root URL that all requests will be sent to.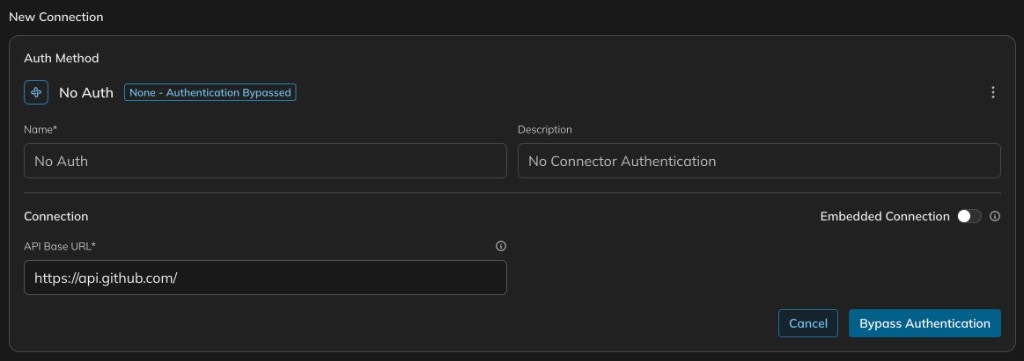
The connection will appear in your list of available connections with its authentication status clearly marked as
bypassed. You can use it in your workflows just like any other connection.